CN=my_user,DC=my_trustelem_domain,DC=trustelem,DC=com
CN=my_group,OU=Groups,DC=my_trustelem_domain,DC=trustelem,DC=com
 ](https://trustelem-doc.wallix.com/uploads/images/gallery/2022-06/scaled-1680-/portldap-radius.png)
[](https://trustelem-doc.wallix.com/uploads/images/gallery/2022-06/setup5-ldap.png)
#### Debug
The connector doesn't appear in the setup page on the admin page
* ping **admin.trustelem.com** on the machine running the connector to verify the outgoing flows
* verify the synchronization ID
* verify the proxy setup
* if the VM is a Windows machine, verify that you clicked on **Validate** on Trustelem Connect program
The LDAP or Radius authentication is no working
* Go on your **Trustelm Logs page** and see if you have **LDAP or Radius** logs. If yes, the connector is working and you should know why the authentication failed:
* if the user is not found, is the login attribute correct?
* if the user doesn't have the permission for the app, is your access rule correct?
* if the user doesn't have a 2nd factor, is your enrollment process correct?
* If your application tries to do a **LDAP search** and doesn't have access rule (LDAP 1 or 2 factors), no users will be found but you will not see any logs because it is not a bug
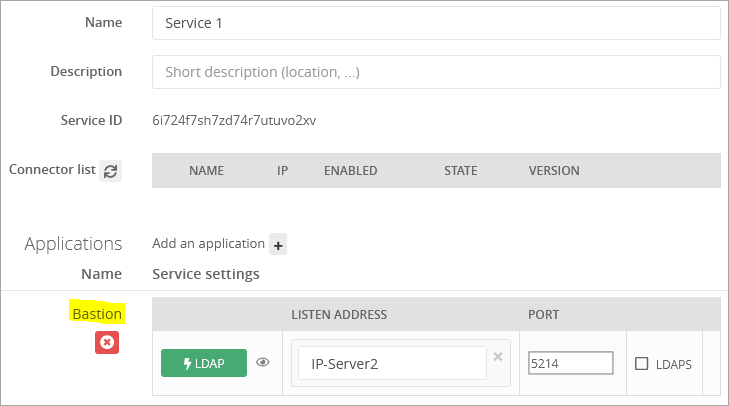
* Go on your **Service setup** and verify if the listen address is correct (should be **\*** if the VM is dedicated to Trustelem)
* On the same page, see the **port** defined and the **setup information** clicking on the **eye button**
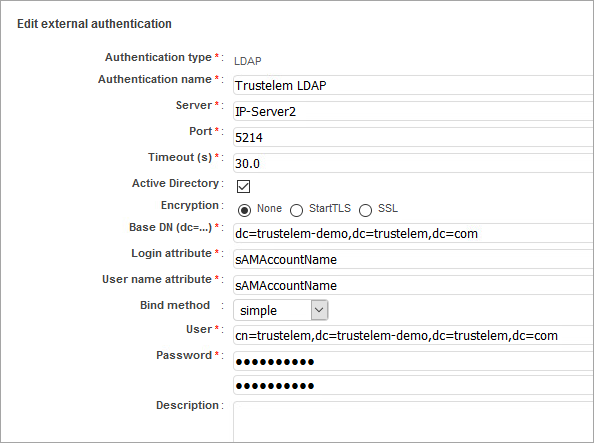
* Verify the setup of the application: server IP, port, DN/account/password for LDAP, secret for Radius
* Verify if the flow from the app to the VM running the connector is opened. If you have a doubt, use **Wireshark** on Windows or **tcpdump** on Linux.
**/!\\** tcpdump displays the flow received, before applying local firewall rules. So if you are on Linux and see the requests, you should verify if there is a local firewall.
](https://trustelem-doc.wallix.com/uploads/images/gallery/2022-06/scaled-1680-/portldap-radius.png)
[](https://trustelem-doc.wallix.com/uploads/images/gallery/2022-06/setup5-ldap.png)
#### Debug
The connector doesn't appear in the setup page on the admin page
* ping **admin.trustelem.com** on the machine running the connector to verify the outgoing flows
* verify the synchronization ID
* verify the proxy setup
* if the VM is a Windows machine, verify that you clicked on **Validate** on Trustelem Connect program
The LDAP or Radius authentication is no working
* Go on your **Trustelm Logs page** and see if you have **LDAP or Radius** logs. If yes, the connector is working and you should know why the authentication failed:
* if the user is not found, is the login attribute correct?
* if the user doesn't have the permission for the app, is your access rule correct?
* if the user doesn't have a 2nd factor, is your enrollment process correct?
* If your application tries to do a **LDAP search** and doesn't have access rule (LDAP 1 or 2 factors), no users will be found but you will not see any logs because it is not a bug
* Go on your **Service setup** and verify if the listen address is correct (should be **\*** if the VM is dedicated to Trustelem)
* On the same page, see the **port** defined and the **setup information** clicking on the **eye button**
* Verify the setup of the application: server IP, port, DN/account/password for LDAP, secret for Radius
* Verify if the flow from the app to the VM running the connector is opened. If you have a doubt, use **Wireshark** on Windows or **tcpdump** on Linux.
**/!\\** tcpdump displays the flow received, before applying local firewall rules. So if you are on Linux and see the requests, you should verify if there is a local firewall.